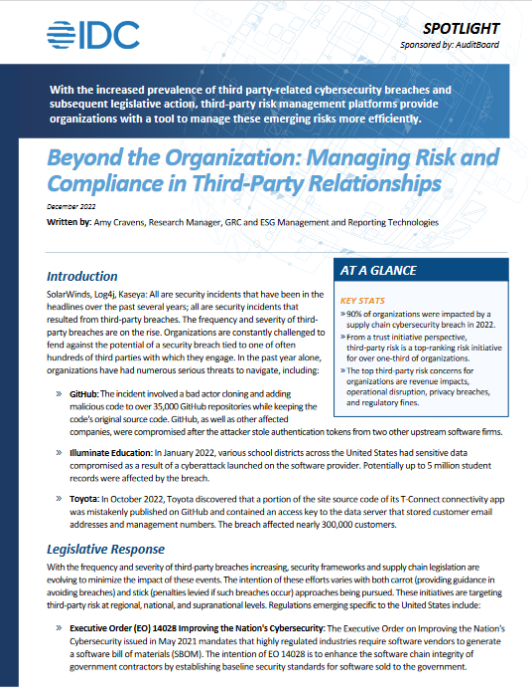
 The frequency and severity of third-party breaches are on the rise: An estimated 90% of organizations were impacted by a supply chain cyber security breach in 2022. Organizations rely on third-party suppliers for products and services necessary to operate; however, these relationships inherently introduce risk to the organization.
The frequency and severity of third-party breaches are on the rise: An estimated 90% of organizations were impacted by a supply chain cyber security breach in 2022. Organizations rely on third-party suppliers for products and services necessary to operate; however, these relationships inherently introduce risk to the organization.
With the frequency and implications of third-party breaches increasing, security frameworks and supply chain legislation are evolving to minimize the impact of these events. The intention of these efforts varies with both carrot (providing guidance in avoiding breaches) and stick (penalties levied if such breaches occur) approaches being pursued.
The current environment of heightened third-party software attacks and subsequent legislative response is elevating third-party risk management (TPRM) as an organizational priority. Modern organizations are increasingly focused on managing business risk to foster resiliency and trust, however, much of the risk that an organization contends with is not internal but stems from third-party relationships.
Research by the IDC found that TPRM is among the top considerations for strategic organizational risk management, ranking fourth in their Future of Trust Survey, behind IT security, data privacy, and operational risk. However, failure to secure third-party relationships can directly impact these other three areas.
TPRM technology solutions can support organizations in managing risk across hundreds, or even thousands, of third-party suppliers. The information management and automation benefits that these solutions provide result in increased efficiency in vendor risk analysis, which, in turn, reduces the potential for a risk event to occur.
Learn more about this emerging risk landscape, the results of the IDC survey, and what organizations can do to protect themselves in Beyond the Organization: Managing Risk and Compliance in Third-Party Relationships.
